Organisations process information in the course of their activities. The availability of information, and its accuracy, has become increasingly essential for successful operations. At the same time, there is an increasing level of activity aimed at obtaining information, either for business gains or with the intent to cause harm. Protecting information is therefore of fundamental interest to all organisations.
INFORMATION SECURITY

A COMPLEX APPROACH
The only way to achieve information security is to strive for comprehensive protection. Information must be protected in all its formats (whether on paper or in an electronic format). The same amount of attention is required in areas relevant to electronic information security: data can be protected through the protection of the applications that process it, the technology that runs the applications and the infrastructure that runs the technology. However, this is of no value if the humans processing the information allow information security breaches to occur (whether intentionally or through ignorance), or if it is possible to circumvent security by exploiting poorly designed processes and weak security controls.


A BROAD PORTFOLIO OF SERVICES
Our experts have a wide range of experience and expertise in implementing information security projects:
- Secure infrastructure construction
- Building and operating high-reliability IT systems
- Hardening existing IT systems
- Design, implementation, and operation of IT security systems
- Information security auditing
- Vulnerability assessment of information systems (black, grey, white box)
- Compliance testing of IT management systems, policies
- Verification of compliance with Act L of 2013
- Data protection compliance (GDPR, Info Act.)
- Information security management
- Development and maintenance of IT security policy environment
- Information Security Officer (IBF) activity
- Data Protection Officer (DPO) services

PROFESSIONAL EXPERTISE
The complex approach to information security requires the knowledge of both industry standards and professional methodologies as well as insight into the specific approach of each vendor. Our experts hold numerous professional certifications.
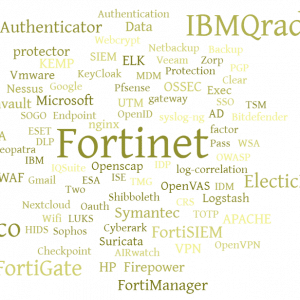
EXTENSIVE PRODUCT KNOWLEDGE
There is a vast number of solutions that can be used in the different fields of information security.
The figure gives you a flavour of some of the solutions we know and apply: